Security
Trending titles
The most talked-about and well-loved Security titles this month.
A Hacker's Mind: How the Powerful Bend Society's Rules, and How to Bend them Back Rating: 4 out of 5 stars4/5How to Be Invisible: Protect Your Home, Your Children, Your Assets, and Your Life Rating: 4 out of 5 stars4/5The Hacker Crackdown: Law and Disorder on the Electronic Frontier Rating: 4 out of 5 stars4/5If It's Smart, It's Vulnerable Rating: 4 out of 5 stars4/5Cyber Warfare: Techniques, Tactics and Tools for Security Practitioners Rating: 4 out of 5 stars4/5Cybersecurity For Dummies Rating: 4 out of 5 stars4/5Data and Goliath: The Hidden Battles to Capture Your Data and Control Your World Rating: 4 out of 5 stars4/5Cybersecurity First Principles: A Reboot of Strategy and Tactics Rating: 5 out of 5 stars5/5The Mathematics of Secrets: Cryptography from Caesar Ciphers to Digital Encryption Rating: 0 out of 5 stars0 ratingsPractical Lock Picking: A Physical Penetration Tester's Training Guide Rating: 4 out of 5 stars4/5Cybersecurity and Cyberwar: What Everyone Needs to Know Rating: 4 out of 5 stars4/5Blockchain Basics: A Non-Technical Introduction in 25 Steps Rating: 5 out of 5 stars5/5Stealing The Network: How to Own the Box Rating: 4 out of 5 stars4/5Liars and Outliers: Enabling the Trust that Society Needs to Thrive Rating: 4 out of 5 stars4/5Blockchain and the Law: The Rule of Code Rating: 4 out of 5 stars4/5Reverse Engineering Code with IDA Pro Rating: 5 out of 5 stars5/5Blockchain For Dummies Rating: 5 out of 5 stars5/5Buffer Overflow Attacks: Detect, Exploit, Prevent Rating: 4 out of 5 stars4/5Digital Forensics with Open Source Tools Rating: 3 out of 5 stars3/5Hardware Hacking: Have Fun while Voiding your Warranty Rating: 4 out of 5 stars4/5Cyberwar: How Russian Hackers and Trolls Helped Elect a President What We Don't, Can't, and Do Know Rating: 4 out of 5 stars4/5Wireless Hacking: Projects for Wi-Fi Enthusiasts: Cut the cord and discover the world of wireless hacks! Rating: 5 out of 5 stars5/5Blockchain Basics: A Non-Technical Introduction in 25 Steps Rating: 5 out of 5 stars5/5Worm: The First Digital World War Rating: 3 out of 5 stars3/5Violent Python: A Cookbook for Hackers, Forensic Analysts, Penetration Testers and Security Engineers Rating: 4 out of 5 stars4/5Microsoft Log Parser Toolkit: A Complete Toolkit for Microsoft's Undocumented Log Analysis Tool Rating: 5 out of 5 stars5/5Bitcoin and Cryptocurrency Technologies: A Comprehensive Introduction Rating: 5 out of 5 stars5/5No Tech Hacking: A Guide to Social Engineering, Dumpster Diving, and Shoulder Surfing Rating: 4 out of 5 stars4/5Schneier on Security Rating: 4 out of 5 stars4/5Web of Deception: Misinformation on the Internet Rating: 4 out of 5 stars4/5
Everything About Security
The Ransomware Hunting Team: A Band of Misfits' Improbable Crusade to Save the World from Cybercrime Rating: 4 out of 5 stars4/5The Cuckoo's Egg: Tracking a Spy Through the Maze of Computer Espionage Rating: 5 out of 5 stars5/5Hacking : Guide to Computer Hacking and Penetration Testing Rating: 5 out of 5 stars5/5The Art of Deception: Controlling the Human Element of Security Rating: 4 out of 5 stars4/5Cybersecurity For Dummies Rating: 4 out of 5 stars4/5Cybersecurity: The Beginner's Guide: A comprehensive guide to getting started in cybersecurity Rating: 5 out of 5 stars5/5Make Your Smartphone 007 Smart Rating: 4 out of 5 stars4/5Social Engineering: The Science of Human Hacking 2nd Edition Rating: 5 out of 5 stars5/5Social Engineering: The Science of Human Hacking Rating: 3 out of 5 stars3/5How to Measure Anything in Cybersecurity Risk Rating: 4 out of 5 stars4/5HACKING: Hacking Firewalls & Bypassing Honeypots Rating: 5 out of 5 stars5/5Certified Information Security Manager CISM Study Guide Rating: 0 out of 5 stars0 ratingsCISA Certified Information Systems Auditor Study Guide Rating: 5 out of 5 stars5/5Cybersecurity: The Insights You Need from Harvard Business Review Rating: 5 out of 5 stars5/5Cybersecurity All-in-One For Dummies Rating: 0 out of 5 stars0 ratingsThe Wires of War: Technology and the Global Struggle for Power Rating: 4 out of 5 stars4/5Practical Ethical Hacking from Scratch Rating: 5 out of 5 stars5/5Amazon Web Services (AWS) Interview Questions and Answers Rating: 5 out of 5 stars5/5CISM Certified Information Security Manager Study Guide Rating: 0 out of 5 stars0 ratingsGoogle Hacking for Penetration Testers Rating: 4 out of 5 stars4/5Hackers & Painters: Big Ideas from the Computer Age Rating: 4 out of 5 stars4/5IAPP CIPP / US Certified Information Privacy Professional Study Guide Rating: 0 out of 5 stars0 ratingsSecurity Engineering: A Guide to Building Dependable Distributed Systems Rating: 4 out of 5 stars4/5(ISC)2 CCSP Certified Cloud Security Professional Official Study Guide Rating: 5 out of 5 stars5/5
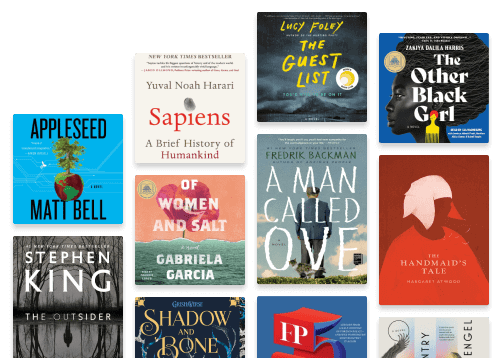
Others you might like
From classic favorites to brand new hits, it’s all here for you to discover.
Recently Added
Tor Darknet Bundle (5 in 1): Master the Art of Invisibility Rating: 5 out of 5 stars5/5Cybersecurity: Learn Fast how to Become an InfoSec Pro 3 Books in 1 Rating: 0 out of 5 stars0 ratingsThe Smartest Person in the Room Rating: 5 out of 5 stars5/5Tor and the Dark Art of Anonymity Rating: 5 out of 5 stars5/5Cybersecurity First Principles: A Reboot of Strategy and Tactics Rating: 5 out of 5 stars5/5Darknet: A Beginner's Guide to Staying Anonymous Online Rating: 5 out of 5 stars5/5HACKING: Hacking Firewalls & Bypassing Honeypots Rating: 5 out of 5 stars5/5Malware Reverse Engineering: Cracking The Code Rating: 0 out of 5 stars0 ratingsBurners and Black Markets: How to Be Invisible on Android, Blackberry & Iphone Rating: 5 out of 5 stars5/5Reconnaissance 101: Footprinting & Information Gathering: Ethical Hackers Bible To Collect Data About Target Systems Rating: 0 out of 5 stars0 ratingsCybersecurity Career Master Plan: Proven techniques and effective tips to help you advance in your cybersecurity career Rating: 0 out of 5 stars0 ratingsBlockchain: Everything You Need to Know About Blockchain Rating: 5 out of 5 stars5/5OSINT 101 Handbook: Expert-Level Intelligence Gathering: Advanced Reconnaissance, Threat Assessment, And Counterintelligence Rating: 0 out of 5 stars0 ratingsISO 27001 Controls – A guide to implementing and auditing Rating: 0 out of 5 stars0 ratingsCryptography And Computer Science: Design Manual For Algorithms, Codes And Ciphers Rating: 0 out of 5 stars0 ratingsISO/IEC 27001:2022: An introduction to information security and the ISMS standard Rating: 5 out of 5 stars5/5Red Team Operations: Attack: Black Box Hacking, Social Engineering & Web App Scanning Rating: 5 out of 5 stars5/5
There’s more to discover in Security
Escape into new titles and new adventures.
Read what you want, how you want
Discover millions of ebooks, audiobooks, podcasts, and so much more with a free trial.
Only $11.99/month after trial. Cancel anytime.